
The Tempest over Leaking Computers
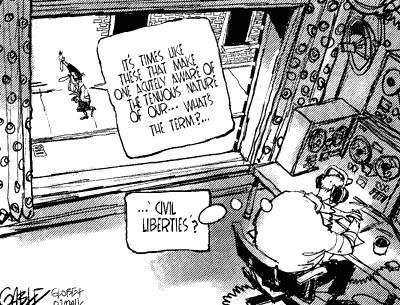
The Tempest (Transient ElectroMagnetic Pulse Emanation STandard) project is a joint research and development effort of the U.S. National Security Agency (NSA) and the Department of Defense (DoD) and has been classified for about 20 years. Even the program's name was classified and unmentionable until only a few years ago. Tempest refers to the investigation and study of potentially compromising electronic signals emitted by computers and other electronic devices. It also involves the development of countermeasures, particularly the shielding of computers and related devices so that the emanations cannot be collected, analyzed, and understood.
September 24, 2005
Stanley A. Klein
Exploitation of Compromising Electromagnetic Emanations
Taxonomy
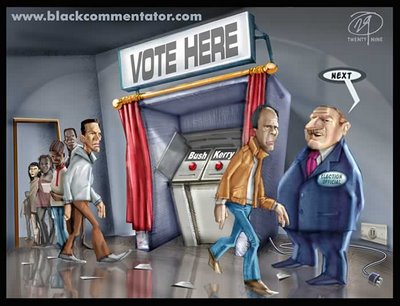
Retail, vote buying, or voter intimidation.
Applicability
DRE voting machines. Possible use against precinctbased optical scan tabulators.
Method
Perpetrator uses compromising electromagnetic emanations from voting machines toreproduce DRE screens in a vehicle near the polling place. Bought or intimidated votersare instructed to make certain combinations of selections and changes to enable theperpetrator to identify which voter is using which machine. Perpetrator watches themachine activity and ensures that voters vote as instructed. This attack effectivelyreturns voting activity to the conditions that existed prior to adoption in the late 1800's ofthe Australian Secret Ballot.Exploitation of emanations from an optical scan tabulator would require either (a) thevoter being instructed to vote in particular ways for offices/issues not of interest to theperpetrator, or (b) administrative records accessible to the perpetrator or an accompliceinside the polling place who can provide information on the sequence of voters whoseballots are being processed.Resource RequirementsThis attack requires development of software to monitor and process the compromisingelectromagnetic emanations. This development has economy of scope; once developed,the hardware and software can be reused in numerous elections. The cost of developingand producing the relevant equipment is likely to be in a multimilliondollar range, butover time the relevant technology is likely to become ubiquitous.
The relevant technology may already exist and be in use within the intelligencecommunity. The feasibility of exploiting compromising electromagnetic emanationsfrom electronic equipment has been rumored since the 1970's. The Defense Departmenthas long had a program called “Tempest” for minimizing compromising electromagneticemanations from electronic equipment. Redacted Tempest documents were posted on theInternet a few years ago as a result of a FOIA request.The technology requirements for accomplishing the attack are likely to include thefollowing:●High capacity software defined radio●Digital signal processing and/or directive antenna technology (such as phasedarrays) sufficient to separate individual voting machine emanations. Forexample, this might be done by using small differences in clock speeds orother processing hardware characteristics of the various machines.●Digital signal processing to reconstruct the internal processing and screendisplays from the voting machine emanations.The software defined radio and high capacity digital signal processing technologies arecurrently available, although not necessarily at low cost and sufficiently small size toallow installation of the necessary facilities in a vehicle. These technologies atappropriate capacities, sizes, and costs are likely to become ubiquitous during the lifetimeof voting machines in current service or currently being designed and purchased.Perpetrators must also have access to a pool of subvertable voters willing to vote in returnfor payment or unable to complain if threatened. Employees, tenants, and those withsimilar dependency relationships are particularly vulnerable.Potential GainOne vote per subverted voter.Likelihood of DetectionThe likelihood of detection depends on the degree of dependency linking the perpetratorto the subverted voters. Countermeasures
Preventive MeasuresApply to voting machines and polling places the Tempest technology and other measuresused by the Defense Department for protecting against exploitation of compromisingelectromagnetic emanations.Use only optical scan machines, and take measures to block the collection of informationthat could identify the sequence of voters whose ballots are being scanned.Detection MeasuresThe attack can not be detected by technical or administrative means. The only possibilityof discovering that it has occurred is if one of the voters reveals the existence of the votebuying or voter intimidation to authorities who are not themselves involved in the scheme.

No comments:
Post a Comment